SOC 2 Type II
Annual third-party audit of security, availability, and confidentiality controls. Report available on trust.etechgs.com.
Etech operates in regulated industries including healthcare, insurance, financial services, and government programs. Our compliance posture is the result of a zero-trust architecture maintained across 7 sites, 3 countries, and 22 years of continuous operation.
OUR APPROACH
Vishal Choudhary, Etech's AVP of Enterprise Technology and Security, joined the company in 2004 as a network administrator and has built the security infrastructure over 22 years. Every site operates under the same zero-trust framework. Every endpoint is managed. Every interaction is logged. The architecture prevents violations before they occur.
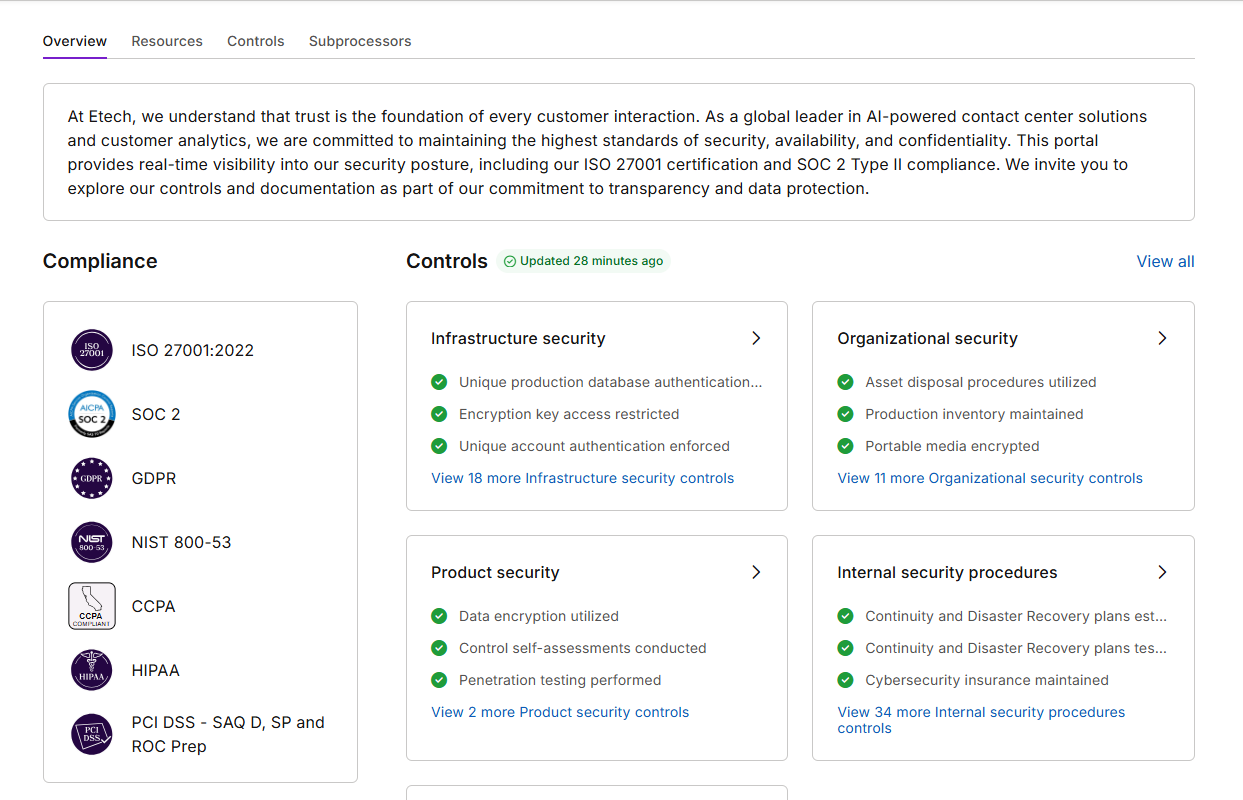
For security teams doing due diligence: the badge grid below links directly to our attestation portal at trust.etechgs.com, where you can access current SOC 2 reports, ISO 27001 documentation, penetration test summaries, and subprocessor lists. No NDA required for standard evidence packages.
CERTIFICATIONS AND ATTESTATIONS
Annual third-party audit of security, availability, and confidentiality controls. Report available on trust.etechgs.com.
Information security management system aligned to ISO 27001 framework. Documentation and controls mapped.
Payment Card Industry Data Security Standard, highest level. All payment-adjacent workflows compliant.
Health Insurance Portability and Accountability Act. PHI handling controls, BAA execution, and breach notification procedures in place.
General Data Protection Regulation. Data processing agreements, subject access request workflows, and EU data handling procedures documented.
California Consumer Privacy Act / California Privacy Rights Act. Consumer data rights workflows implemented.
Telephone Consumer Protection Act. 14.2M interactions processed with zero TCPA violations. Consent capture and DNC scrub at the stack level.
Gramm-Leach-Bliley Act Safeguards Rule for financial services programs. Customer financial information protection controls active.
Minority Business Enterprise certified. Procurement diversity qualification.
View live attestation evidence, subprocessor lists, and penetration test summaries at trust.etechgs.com
Visit trust.etechgs.comSECURITY CAPABILITIES
Built and maintained by an in-house team of IT and security professionals across Microsoft, Linux, Cisco, and Fortinet platforms.
Zero-trust architecture across all 8 sites. VPN segmentation, Fortinet firewall infrastructure, endpoint management, and real-time monitoring. Network traffic logged and analyzed continuously.
PHI, PCI, and PII redacted at point of capture using NER-based models. No sensitive data stored from day zero on regulated programs. Redaction covers voice transcripts, screen recordings, and chat logs. Third-party attested.
Virtual Desktop Infrastructure for regulated programs. Agents access client systems through secured VDI sessions. No data touches local endpoints. Dealer and consumer queue separation by default on multi-brand programs.
24/7 SOC monitoring. SIEM integration. Automated threat detection with defined incident response playbook and SLAs. Penetration testing conducted annually by independent third parties.
All devices managed centrally. USB ports disabled. Screen capture blocked. Bring-your-own-device prohibited on regulated programs. Patching automated across Microsoft, Linux, and Cisco platforms.
Role-based access with multi-factor authentication. Least-privilege model. Segregation of duties for system administration. Active Directory and SSO integration across all platforms. Access reviews quarterly.
INDUSTRY-SPECIFIC COMPLIANCE
LIVE ATTESTATION EVIDENCE
Our trust portal at trust.etechgs.com provides live access to SOC 2 reports, ISO 27001 documentation, penetration test summaries, subprocessor lists, and current attestation status. No NDA required for standard evidence packages.
COMMON QUESTIONS
Yes. Available at trust.etechgs.com. No NDA required for the standard report.
No. On healthcare programs, PHI is redacted at point of capture. No PHI is stored from day zero.
Defined in our incident response playbook. Available upon request through trust.etechgs.com.
Subprocessor list is published at trust.etechgs.com and updated with advance notice per contractual requirements.
We will walk you through the architecture, share evidence packages, and answer every question your compliance team has.